Participate In Qitchain Network
The Qitchain Network is a genius that can reduce energy consumption and allow the participation of miners’ self-made common components while maintaining a high level of difficulty to assure the system’s stability.
Qitchain Network uses the CPoC consensus algorithm, which is a highly decentralized consensus method.
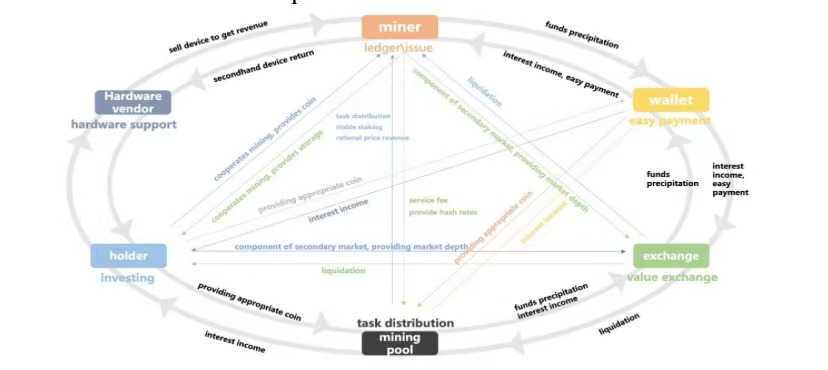
There are six kinds of roles that are given to the participants in the Qitchain network:
• Mining Pools
• Miners
• Coin Holders
• Wallets
• Exchanges
• Hardware Service Providers
The inner economic cycle and the input of external resources both allow the network to extend and evolve, owing to the ecological value game based on the CPoC consensus mechanism. All participants will have a more positive response to the overall system as precipitation continues and network value rises. It is once again boosting the network’s value that is increasing in a beneficial way. The CPoC consensus will allow miners, mining pools, foundations and other participants to have a positive business game so that the entire system will always have the more dominant temporary commercial vested interests. This vested interest will continue to change with the time, price mining difficulty and other variable conditions; it is done to promote the entire ecology invisibly.
We know that the traditional POW consensus network has four characteristics namely:
1. Has the cost of doing evil
2. The cost of minting is high
3. The difficulty of obtaining continues to increase
4. There is a certain value reduction in mining equipment
Eventually, participating in a POW network will also become a low-value behavior. The short-term profiteering is only due to the insufficient scale on the one hand, the asymmetry of the value fluctuation, and the increased curve of mining equipment on the other hand. Because the hardware is largely linear in value preservation and power consumption is low in the CPoC consensus method, the weight of future symbiosis ecological miners to gain additional values for free and with nearly no risk cost. The risk cost holds assets to prevent the malicious actions of miners.
Meanwhile, the CPoC consensus system attaches great importance to the threshold-free release of issuance rights and bookkeeping packaging rights, which determines the fairness of this system.
Based on the PoC consensus, Qitchain Network designed a conditional proof based on the pledge model. This conditional model is jointly formed by two parties: the miner who produces the block and the top 10 users of the pledge amount. We use it to represent the block reward finally obtained by both the miner and the top 10 users of the stake after digging a block. The miner obtains mining information from the wallet, including the newly generated signature, base target, and the height of the next block. Before the wallet sends this information, it creates a signature by producing the last generated signature and plot id. After that, run this method through Shabal256 to obtain a new 22 hash. The miner will use the new 32-byte generation signature and 8-byte block height and put them together as the seed of Shabal256 to calculate the hash.
Mining pool node contains the mining pool protocol and the mining sub-nodes belonging to it. Local miners in hard disk generate Plot file contains a hash value of its public key, integrated Shabal algorithm to fill the hard drive. The larger the hard disk capacity, the more hash values are filled, and the higher the probability of winning the difficult competition. The hash algorithm adopts the Shabal256 algorithm, which is resistant to ASIC.
Miners transfer operations between wallets. Wallet/Client provides users with inquiries and management of accounts and nodes. A wallet contains a series of key pairs, and each key pair includes a private key and a public key. ‘k’ represents the user’s private key, usually a number whereas ‘K’ represents the public key generated by ‘k’ through the elliptic curve multiplication algorithm. ‘A’ represents the address generated by ‘K’ through the hash function.
While participating in the block generation, miners only need to send the block content and two parameters to the wallet node. The wallet can calculate the entire Nonce value, simultaneously, after each node on the network receives apiece block, it calculates whether its deadline is authorized by calculating this nonce. After the wallet receives the information submitted by the miner, it creates a corresponding nonce to find and verify the deadline. Then the wallet will check the time remaining in seconds.
If a valid block from another wallet is received on the network before the deadline arrived, the wallet will discard the previously submitted mining information. If the miner submits new information, the wallet will create a nonce and check whether the deadline value is lower than the previous deadline. If the new deadline is lesser, the wallet will exercise that deadline and the wallet starts to construct a new block. The wallet tries to include as many transactions as possible until it reaches the upper limit of 2M size or all transactions are processed. The wallet checks the legality of all transactions received, such as whether it has a valid signature, correct timestamp, legal input and output, etc. The wallet will also count the amount and cost of all added transactions.
The blockchain system based on POW consensus needs to consume a lot of hardware resources and power resources to maintain its security. So miners cannot establish mutual interests and mutual recognition, and the consumed resources cannot be deposited in its value system. The value of this part is being withdrawn from the POW system all the time. Without value-driven, it is difficult to update key technologies thus failing to obtain long-term, effective development and iteration. It is easy to cause bifurcation in the follow-up.
Above all, for the CPoC system, hard disk power consumption is low, and miners’ income will be clearer. The linear hedging rate of computer hardware guarantees that miners can obtain value with relative safety and capital preservation.